Lately, one of my favorite kinds of entertainment has been hackthebox.org. HTB has different kinds of challenges: single machine pentest, network pentest, reverse engineering challenges, pwn games, etc. Recently, HTB announced the availability of pwnbox: a service that provides a web based ready-to-use environment.
#HackTheBox Presents Pwnbox 📢#Hack all #HTB labs directly from your browser ANYTIME, ANYWHERE! Start PwnBox NOW 🤩 https://t.co/fArbAqDXo6#CyberSecurity #CyberSecurityTraining #Pentesting #Infosec pic.twitter.com/gnF6K7uDYr
— Hack The Box (@hackthebox_eu) May 27, 2020
Under the hood, pwnbox is based on parrot and runs a vnc server. theGuildHall documented how to create your very own pwnbox.
This post describes the setup that allows me to use my iPad to solve these kind of challenges.
my ipad and my pwnbox
the pwnbox:
- only open port to the world is ssh;
- is running TigerVNC, which supports dynamic desktop resize
- is running easy-novnc
the ipad:
- blink for ssh access
- Jump Desktop for VNC access. It supports ssh tunneling and server side desktop resize. An alternative could be enabling local port forwarding and just rely on novnc (also supports server side desktop resize).
the two environments look like this (iPad screenshots):
spinning up a pwnbox
When I’m traveling, I run a pwnbox virtual machine on DigitalOcean. I create my pwnbox when I need it from a custom image that I update once in a while.
Since I want the VM creation to be quick and I don’t care how long the base image takes to build, most of the tools I need are installed to the base image.
Once I have the base image uploaded, I use an ansible playbook to create and setup the vm:
- create a droplet
- create/update a DNS A record that points to the droplet’s IP address
- configure my user
- synchronizes ssh/authorized_keys from root (these were previously configured by cloud-init)
- copy my dotfiles
- copy my HTB openvpn configuration file
The droplet creation + setup usually only takes a couple of minutes and leaves me with a ready-to-play environment.
When I’m not traveling, I use the same base image to start a VM on my linux desktop with a cloud config drive attached.
using the pwnbox
reverse engineering / pwn / binary exploitation challenges
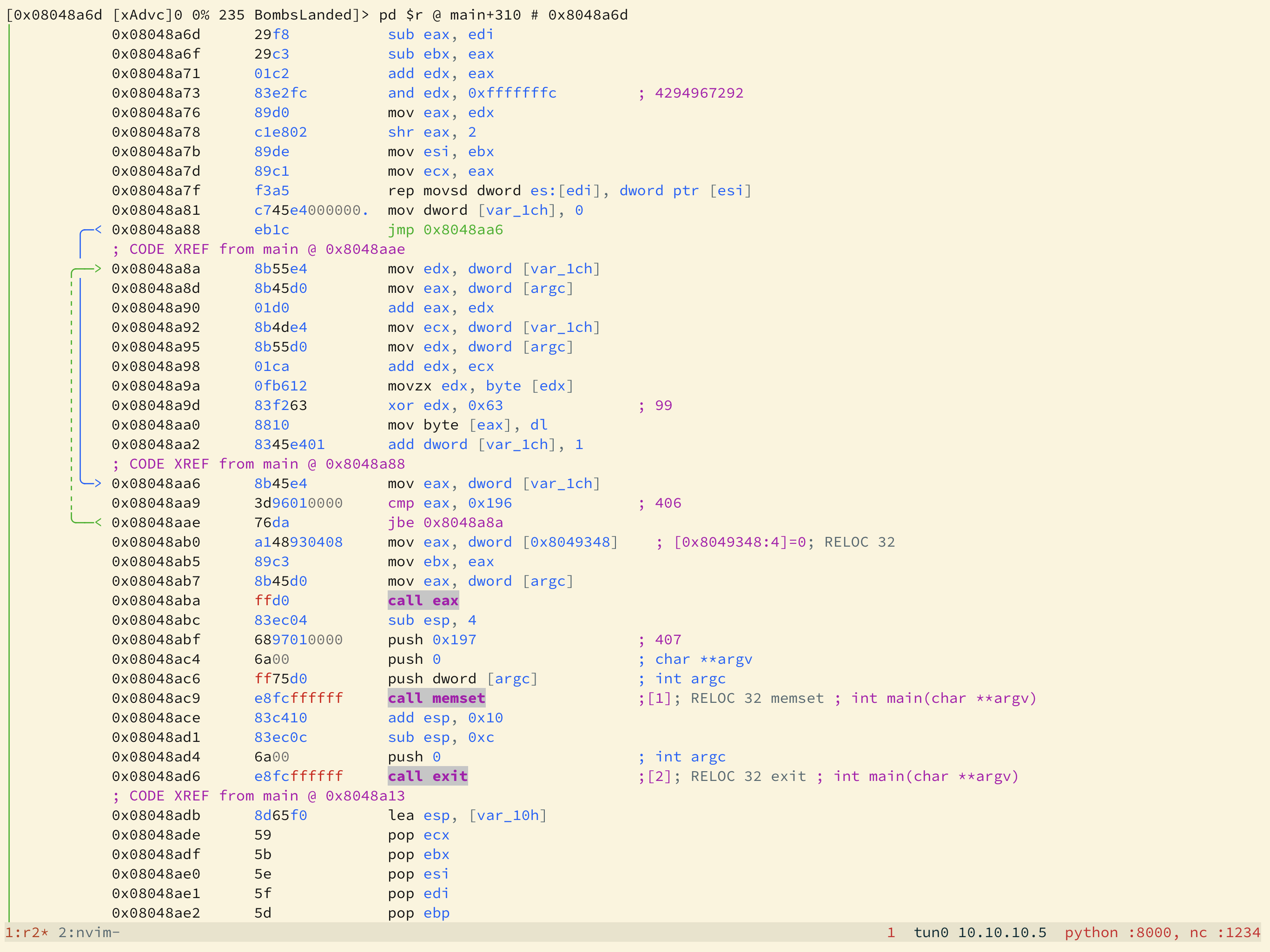
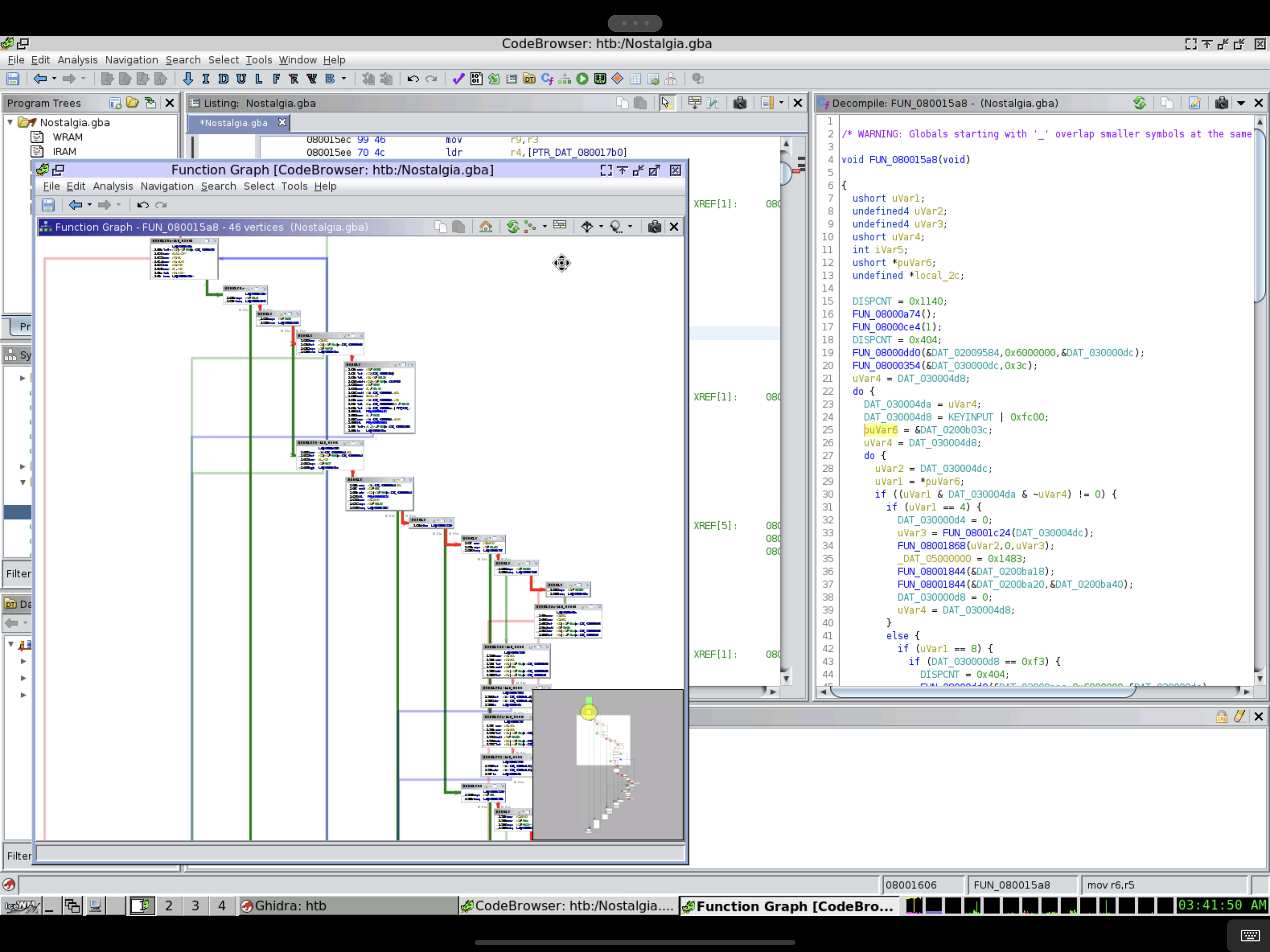
For trivial binaries, I use radare as disassembler and debugger. I’ve been experimenting with r2ghidra-dec and so far I don’t feel strongly about it. I use pwntools as a platform for most of the exploits I write and sometimes I automate my debugging sessions with r2pipe. It doesn’t feel as integrated as pwntools+gdb, but I really enjoy using radare.
For less trivial binaries, I use IDA or ghidra. When I just need a graphical graph overview, I use Cutter. I use pwntools+gdb integration to do any exploit writing and testing. Pwntools integration with tmux is one of my favorite features. r2pipe is my favorite tool to solve reverse engineering challenges that can be solved with a breakpoint+continue loop.
Nowadays, my .gdbinit just sources gef. My radare2rc is very boring, it’s less trivial feature is set of custom visual mode layouts that enable register and stack telescoping.
pentesting
I have a set of scripts to avoid typing the same nmap and masscan oneliners over and over again. And I have another set of wrapper scripts for wfuzz (I’m slowly adopting fuff) and gobuster. Very often, my recon process develops like this:
- I run
quick-recon $targetand look at the results - it usually takes 2 or 3 minutes; - Unless there is something very obvious, I batch some
slow-recon --$modifier $targetjobs and leave my pwnbox unattended; - When I come back, sometimes hours later, I have a bunch of recon output logs to investigate.
- Lazy ? Yes. Time efficient? Yes.
For most of the challenges, gaining the foothold is done thru something that speaks http.
- I start by doing some old boring web browsing and I use firefox for this.
- I start burpsuite and run
curl -x $http_proxy $(cat valid_urls.log); I like to have burpsuite’s sitemap populated. - As much as I would love to only rely on zaproxy or mitmproxy, I’m much more efficient with burpsuite, so it has been my favorite exploration tool.
Exploitation varies from target to target, but there are a couple of repositories and tools I’ve installed in my base image:
I also find myself browsing gtfobins very often.
Other miscellaneous shortcuts to avoid some repetition:
- Seclist’s rockyou.txt is unpacked and my
.zshenvsets$ROCKYOUTXTaccordingly; - Some aliases to netcat LinPEAS to a specified host:port
- A script to start
python -m http.serverin a directory with LinPEAS, shell.php, etc.
deployment scripts, etc
My base image builder can be found here.
additional notes
-
The VNC session is usable, but not great:
- In theory it should be possible to have a full HiDPI session, but I’ve not tried yet. Having low latency is very important to me and this setup has been working quite well even under flaky connectivity.
- Is VNC the best we can have in 2020? I feel RDP has been decades ahead for decades.
- I have been wanting to experiment having a virtual desktop size much larger than the physical screen resolution. This could be useful to visualize IDA and ghidra graphs.
-
I use nixos on my linux machines and I’ve a pwnbox branch using home-manager. I would love to have a full nixos installation, but is very convenient to have ld.so in the expected path for pwn and reverse engineering challenges. Home-manager solves some of my pain with transitive dependencies and I might adopt it as my pwnbox configuration driver.
-
Sometimes is useful to have a quick synchronization mechanism that “just works”. My dotfiles pack include
$HOME/.config/syncthingwithout the index directories (more info here); I’m able to start syncthing and have the shared folder created and synchronized right away.
Feel free to drop me a line if you have any questions, comments or questions.
Happy hacking!